HUMAN ERROR
A Collection of Projects that Emphasize Things We Do Wrong With Technology and the Internet.

A Collection of Projects that Emphasize Things We Do Wrong With Technology and the Internet.

Today we are often confronted with computer interfaces that are built to be “easy to use”, but in reality, are more confusing than ever. “Human Error” consists of software projects and hardware devices that integrate elements of human error into their design to provoke and materialize human frailty when it comes to operating digital devices and interfaces. Perhaps by designing these "human" elements into user interfaces we will move closer to creating machines that could pass the "Turing Test".
James Reason, former Professor of Psychology at the University of Manchester, coined the term “Human Error” in the late 1980s. Reason quantified human error in two distinct categories that of the (1) person approach and the (2) system approach. While the person approach examines errors of individuals in areas of deficit such as forgetful-ness, carelessness, negligence and similar, the system approach takes a wider stance and blames human error on organizational mishaps or structural systems that are difficult to master. While chances for human error are almost infinite, they can also broadly be categorized into two different types: skill-based and decision-based errors. The difference between these two definitions focuses on whether or not the person had the required knowledge to perform the correct action. The projects in this series focus on the “person approach” where most of the error correctable tasks could have been avoided entirely.
A password field that automatically changes your chosen password to the word "Password" when submitted.
A software application that repeatedly dims your display to 50% every 5 minutes.

An iOS app that removes the numbers from the dialing interface forcing users to dial with (and second guess the existence of) letter combinations.
A modified printer that continually causes a paper jam when in use.

A web entry form built to cause identity theft.

A power strip with too many plug spaces so that it cannot fit anything.
A software bot that automatically clicks on suspicious links.

A monitor that continually changes source to "no-signal".
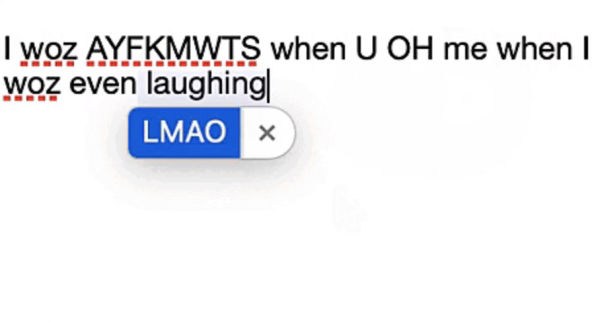
A hacked auto-correct engine that integrates wrongly used abbreviations into typed messages.

A mouse that only clicks "right-click".
A software agent that changes all online text communication to "ALL CAPS".
A mobile app that calls a random number from your contacts list when it senses a low light environment such as a pocket or bag.
A web camera that will only take a photo if you are not looking at it.

A power switch that can only turn a device "off".

An email client that forces users to CC unintended recipients when writing an email.

A website that demands ransomware to show you that it is ransomware.

A software agent that deletes random text from writing applications.

An email client that turns every outgoing email into spam.

CRWDDSTRIP is a modified powerstrip that contains too many plug holes and spaces to allow for more than a single plug to fit. This design forces users to try and plug in their device and fail every time. This form of "Human Error" is common with people who use multiple devices and never have enough plugs to plug them all in. Power strips are often overloaded to the point where they become unsafe since they are drawing too much current that their available connection can handle.
Description
Password is a web form that asks users to type in a password and click the “Set My Password” button. Once clicked, the new password is submitted to the server and automatically changed to the word “Password”. According to a 2019 HYPR study on password creation, 72% of people reuse passwords for their personal accounts. The word “Password” is still the 4th most common password used by people behind “123456”, “123456789”, and “qwerty”. Since the use of the word “Password” as a password is a choice most of us have, and due to this word’s proclivity to be guessed by potential hackers, the fact that this word is still being used is one of “Human Error” that could easily be rectified.
System
The system uses javascript to detect what a user types in and based on the input, the password field is changed to the word “Password” when the button is pressed.
Demo
Try out Password here.
Video Description
“Lttr Dial” consists of an iOS app that removes the numbers from the phone dialer application. Instead of typing in someone’s numbers, users are forced to remember the corresponding letter combinations associated with each number key to dial the correct number. As we often not only forget phone numbers, trying to remember the corresponding letters can be a challenge even for the most versed cellphone user. The app is a critical instigator that highlights our continued reliance on the cloud and saved data to compensate our own innate memory abilities.
More Info

Identity theft begins when someone takes your personally identifiable information such as your name, Social Security Number, date of birth, your mother's maiden name, and your address, to use it without your knowledge or permission. Identity theft is so prevalent online that there’s a new victim of identity theft every 2 seconds. During the first half of 2021, 118.6 million people had their records exposed in data breaches and consumers lost more than $56 billion to identity theft and fraud. Theft ID is a web-based form that includes all of the necessary elements to cause Identity theft and relies on "human error" or the inability of individuals to determine whether or not they are giving up too much of their personal information to reliably trust this particular web form. You can try the form out here to see if you can stop this form of "Human Error".
THEFT ID DEMO

Common computer errors happen when people wrongly click on the mouse buttons causing a “right-click” when they intended a “left-click”. On the first commercial Apple mouse, Bill Atkinson decided on using the “double click” to run applications while the single click was used for selecting an application’s icon. While the “right click” was first introduced in the Small talk environment on Xerox’s Alto computer in the mid 1970s to bring up a “contextual menu”, it was popularized by Microsoft with the launch of Windows 1.0 in 1992.
“RightCLICK” is an artwork consisting of a USB mouse with two buttons that are modified so that both buttons function as a right click. Because of this mod, users are unable to click on any objects on their computer desktop, bringing up the contextual menu on every click. This form of “Human Error” highlights our continued inability to use basic computer-human-interfaces, causing us to fail and lose patience at every interaction point.
We are often confronted with computer interfaces that are built to be “easy to use”, but in reality they are more confusing than ever. Most of us have run into the problem where we have trouble seeing what is on the screen due to the brightness level being too low but we typically ignore this feature / discrepancy because it’s too much work to change or we are too lazy to correct the problem. Human Error is blamed on not changing the brightness level which can result in poorer eyesight for the user as well as added strain on brain capacity and attention.
“Dim” consists of a software application that repeatedly dims the display of users to 50% every 5 minutes. Users must correct the dimness to 100% in order to get back to work, knowing that their screen will return to lower brightness shortly. Whether they choose to fix it or choose to ignore it, the resulting error will be caused by their ability to inability to attend to their computer. Yet another aspect of human / machine error.
Download Dim
Version 1.0, for Mac OS 11 and higher.
More Info
Video Description
We are often confronted with our monitors and displays (whether they are televisions or computers) showing a “no signal” error on their screen. Although one of the easiest errors to fix, most people still have trouble navigating the un-standardized array of monitor and television firmware and user interfaces. Despite a plethora of manuals, training videos, and booklets available to help, people are continually unable to find a signal on their displays.
NoSGNL is a modified monitor that continually changes the chosen signal to an empty source or “No Signal”. Despite the user’s best intentions to connect their device to the display, NoSGNL will constantly show a “No Signal” indicator forcing them to try again. This form of “Human Error” remains a mainstay in the world of consumer electronics and hardware devices.
Video Description
PPRJM (Paper Jam) is a printer that has been modified to continually cause a paper jam. This form of “Human Error” is something that continues to plague people who think they have correctly loaded paper but have failed due to their inability to follow directions. The average amount of paper waste that comes from an office annually is 10,000 sheets. Whether the paper is wrongly put into the printer or used erroneously and then discarded, this amount of waste is troubling even for the environmentally conscious. Recycling levels in the U.S. are only at 21.4% and Americans throw away enough office paper each year to build a 12 foot high wall from Seattle to NY annually.
The system uses an HP OfficeJet Pro 8035e printer with custom electronics and a motor that purposely displaces the paper in the printer’s loading tray. Since the paper enters the printer at an off angle, it will never complete the print correctly, thus resulting in a jam.

While composing emails and other writing on computers there are no longer any text editors without the feature of “auto-correct”. Whether we like it or not, our text is changed, highlighted, or modified by default (unless we purposely turn it off) resulting in perfect spelling across all writing applications. As we currently live in a hyper-capacity, high speed information context where words and phrases must be shorted to fit within Twitter’s 280 character limit or crafted in short sound bites as to not overcrowd our already shorted attention spans our vocabulary is changing. A common change is people writing #hashtags or trying to use common abbreviations to shorten their messages. “Human Error - Auto-CRCT” is a text editor that integrates wrongly used abbreviations into typed messages, resulting in misconstrued messages and typos in non-existent word shorteners.
Video Description
PCKTDial is a phone application that automatically calls a random person in your contact list when the phone senses low light levels as if it was in a pocket or handbag. Typically when we least expect it, our phones tend to dial others without our knowledge resulting in wrongly made cellular calls or as they are commonly called “butt dials” or “pocket calls".
This “human error” is a common problem for people who are unfamiliar with the technology they carry around with them and unable to “lock” or turn off their phones when not in use. Because of this “human error”, calls are made without their knowledge, causing confusion from those on the receiving end of the call.
In 2015, Google completed a research study about the prevalence of people calling “911” from “Butt Dials” or accidental calls and found this to be a serious problem with modern smartphones. The study discovered that one of every five calls to emergency services was due to "accidental dials” or “butt dials” and 30% of those calls originated from wireless devices and smartphones. Without software fixes to existing operating systems to stop this form of calling, the problem will persist unchecked. PCKTDial integrates this form of human error into its design to call to attention a problem that occurs daily with no end in sight.
Video Description
"CAPSLCK - human error” is a software work that changes typed text to ALL CAPS. This is an especially common "human error" people make when writing messages such as emails and texts because it creates the illusion that one is “screaming” at the other person through capitalization emphasis. Researcher Maria Heath examined how using caps lock when composing social media posts functions as a “negative strengthener” and how non-standard orthography such as the use of caps lock can be read as both positive and negative tonal outputs by the author. Positive in relaying messages such as "FANTASTIC" or "HOOORAY" and negative as in "GOOD JOB SCREWING UP" as a stand in for shouting. This confusion as well as its subjective interpretation can result in thoughts of “anger” and “yelling” or a general upscaling of the emotive content of the message. Without having control over formatting text as non-caps or ALL CAPS highlights this "human error" and forces the user to rethink both the context and tonal language of their message and begin to change their behavior.
Writing an email is now as common as signing a document or making a phone call. We think nothing of it and the process is typically second nature to most of the technologically literate. Despite this common process, people still make the error of mistakingly carbon-copying or CC-ing addresses of people that the message was unintended to reach. In 2020, Tim Sadler, the CEO of Tessian, a cloud-based email security platform started in 2013 that prevents advanced email threats, said that “Human error is the leading cause of data breaches, because people make mistakes and break the rules. In many cases, people may not even realize they’re doing anything wrong. If businesses want to keep their data safe, they need to start at the human level and create a people-centric approach to cybersecurity that focuses on educating and protecting their employees.”
Human Error - Spam Mailer” is a software artwork that will automatically turn any typed email into one that will end up in the spam folder of the recipient. The software finds the most egregious spam words and automatically attaches and inserts them along with extra images, links, and embedded code into the message in order to weigh it down with problematic contents that spam filters will process.
According to Statista, “between October 2020 and September 2021, global daily spam volume reached its highest point with almost 283 billion spam emails from a total of 336.41 billion sent emails”. “Human Error - Spam Mailer” is a software artwork that will automatically turn any typed email into one that will end up in the spam folder of the recipient. The software finds the most egregious spam words and automatically attaches and inserts them along with extra images, links, and embedded code into the message in order to weigh it down with problematic contents that spam filters will process. Some of these spam related keywords include“100% More”, “Extra Cash”, “Earn Money”, “Free Trial”, “Save big Money”, “Once in a Lifetime”, “Miracle”, Incredible deal”, and more.
The application will randomly select key spam words that any filter will catch and add them to your outgoing email. The project will also choose from a selection of suspicious links and images and add those to all outgoing email messages as well. This addition of material on emails will guarantee that they will be caught in the email client’s “spam filter” and not delivered to the recipient.
Spam Keywords
100% more, 100% free, 100% satisfied, Additional income, Be your own boss, Best price, Big bucks, Billion, Cash bonus, Cents on the dollar, Consolidate debt, Double your cash, Double your income, Earn extra cash, Earn money, Eliminate bad credit, Extra cash, Extra income, Expect to earn, Fast cash, Financial freedom, Free access, Free consultation, Free gift, Free hosting, Free info, Free investment, Free membership
Free money, Free preview, Free quote, Free trial, Full refund, Get out of debt, Get paid, Giveaway, Guaranteed, Increase sales, Increase traffic, Incredible deal, Lower rates, Lowest price, Make money, Million dollars, Miracle, Money back, Once in a lifetime One time, Pennies a day, Potential earnings, Prize, Promise, Pure profit, Risk-free, Satisfaction guaranteed, Save big money, Save up to, Special promotion, Act now, Apply now, Become a member, Call now, Click below, Click here, Get it now, Do it today, Don’t delete, Exclusive deal, Get started now, Important information regarding, Information you requested, Instant, Limited time, New customers only, Order now, Please read, See for yourself, Sign up free, Take action, This won’t last, Urgent, What are you waiting for?, While supplies last, Will not believe your eyes, Winner, Winning, You are a winner, You have been selected, Bulk email, Buy direct, Cancel at any time, Check or money order, Congratulations, Confidentiality, Cures, Dear friend, Direct email, Direct marketing, Hidden charges, Human growth hormone, Internet marketing, Lose weight, Mass email, Meet singles, Multi-level marketing, No catch, No cost, No credit check, No fees, No gimmick, No hidden costs, No hidden fees, No interest No investment, No obligation, No purchase necessary, No questions asked, No strings attached, Not junk, Notspam, Obligation, Passwords, Requires initial investment, Social security number, This isn’t a scam, This isn’t junk, This isn’t spam, Undisclosed, Unsecured credit, Unsecured debt, Unsolicited, Valium, Viagra, Vicodin, We hate spam, Weight loss, Xanax, Accept credit cards, Ad, All new, As seen on, Bargain, Beneficiary, Billing, Bonus, Cards accepted, Cash, Certified, Cheap, Claims, Clearance, Compare rates, Credit card offers, Deal, Debt, Discount, Fantastic, In accordance with laws, Income, Investment, Join millions, Lifetime, Loans, Luxury, Marketing solution, Message contains, Mortgage rates, Name brand Offer, Online marketing, Opt in, Pre-approved, etc...
-----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
AutoDelete is a software agent that will randomly delete large sections of written text from your text editor while you type and then auto-save the edit. Mistaken deletion is a form of human error that most people using computers experience frequently when they are engaged in long writing projects or assignments and an unknown mishap occurs. This is usually because of a power failure, a mistyped set of keys, or an errant keyboard press on highlighted text, but this type of error is extremely common for both novel and advanced computer users. Human Error - AUTODelete will also disable the “Undo” function of the writing software making it impossible to retrieve lost work. Without this fail safe, human error gains more importance in the inevitable function of trying to maintain a failsafe work environment on and offline.
Everyday we encounter a plethora of links coming from incoming emails, instant messenger clients, SMS messages on our phones, and those on websites and apps we visit. Due to the enormous amount of links we are exposed to on a daily basis, the chances of us clicking on adversely represented links is very high. The term “MALware” comes from a combination of the terms, “malicious” and “software”. While different from a virus, MALware cannot corrupt files in the same way as viruses and instead intercept user data and send it to a third party. “MALware” is also different from “Ransom ware” which hijacks your computer and forces you to pay a ransom to get your data back from the attackers.
Mal directs its approach by examining how people respond to "Phishing Scams". Phishing scams include links that are masked as destinations and sites that are trusted but include code that steals personal information. According to the FBI’s Internet Crime Complaint Center it was reported that people lost $57 million to phishing schemes in one year. These spoofs often use subdomains to imitate the legitimate links or links that have added subdomains such as a common one spoofing Chase Bank like “cha.se.com", or “chase.anydomain.com". Be sure to double check for hidden additional characters, or lookalike characters as well: cha-se.com, or chas3.com.
MAL is an artwork and bot that will automatically click on links based on a list of specific criteria that would specify that link to be fraudulent. This form of “Human Error” occurs constantly and the software, not the human, is typically blamed for these mistakes. MAL shows how human error could be designed into future forms of software to emphasize human frailty when using software systems.
A Few Criteria that expose suspicious links:
1. If the text link is different from the HTML link.
2. if the word in the link is too close to an existing URL.
3. If the embedded link is too long (longer than the text link).
4. If it links to a suspicious root domain.
5. If the link is masked by a link shortener.
6. If it links directly or redirects to a file rather than a web page.

As the world shifts a model of digitization of financial documents, important company and organizational data, employee records, and a general move away from paper bookkeeping, the proclivity that this information could be compromised by external actors increases. As we trust the “cloud” daily with more of our important and personal information, the chance that criminals could infiltrate these seemingly secure data repositories remains an imminent threat.
Human Error - DemandWare is a website paywall that demands users “Ransom Ware” in order reach their files, only to reveal that instead of giving them access to the the files they seek, they are instead given access to another paywall of “Ransom Ware”. This loop continues ad infinitum until all bank accounts are completely drained. This form of human error in giving into criminal demands for a "ransom" is becoming more and more common and will hopefully end soon.

Despite the simplicity of a simple on/off switch, many people are still confronted with the “human error” of not being able to turn their devices “on”. “Human Error - OffSwitch” is a custom designed power switch with two “off” positions. When using this switch, a person will be unable to turn “on” anything connected to it. This type of mistake plagues even the most tech savvy individuals who often have issues not only trying to connect their devices, but when trying to get them to turn on and activate is a daily struggle. With “OffSwitch”, they will never be able to turn on their device, thus adding to this common “human error”.
Jonah Brucker-Cohen, Ph.D., is an artist and an Associate Professor in the Department of Journalism and Media Studies at Lehman College / CUNY in the Bronx. He received his Ph.D. from Trinity College Dublin. His work focuses on “Deconstructing Networks” with works that challenge and subvert accepted perceptions of network interaction. His artwork has been exhibited at venues such as SFMOMA, Canadian Museum of Contemporary Art, MOMA, ICA London, Whitney Museum of American Art, Palais du Tokyo, Tate Modern, Ars Electronica, Transmediale, and more. His artworks, “Bumplist” and “America’s Got No Talent” are in the permanent collection of the Whitney Museum of American Art. He has written for WIRED, Make, Gizmodo, Neural and more. His Scrapyard Challenge workshops have been held in over 15 countries in Europe, South America, North America, Asia, and Australia since 2003.
EMAIL: jonah at coin-operated.com
PUBLICATIONS
1. Brucker-Cohen, Jonah,“Human Error: Projects That Emphasize “Misuses”
of Technology” Artist Talk”, International Symposium on Electronic Art, (ISEA 2022) , June 2022, Barcelona, Spain.
2. Brucker-Cohen, Jonah,"Human Error, A Collection of Work that Highlights Our
Misuse of Technology and the Internet”, EVA London 2022 ,
London, United Kingdom.
3. Brucker-Cohen, Jonah,"Human Error How Integrating Common Errors Into User Interfaces Can Challenge Our Perceptions and Change Design Thinking”, chapter in Green Revisited. Encountering Emerging Naturecultures in Art and Research Paperback, RIXC, Riga, Latvia, 2022.
SHOWS
1. Human Error: A Collection of Projects that Emphasize Things We Do Wrong With Technology and the Internet.
Weird Media Exhibition
Winona State University, Winona, Minnesota, June 24-26, 2022.
Built with
Offline Website Creator